Technical and Organizational Security Measures
These Technical and Organizational Security Measures (“Security Measures”) are incorporated into and form part of your agreement with Monte Carlo Data, Inc. with respect to your use of the Monte Carlo Service (the “Agreement”).
The Security Measures set out the security features, processes, and controls applicable to the Service, which employ industry standard information security best practices.
1. Definitions
The following terms have the following meanings when used in the Security Measures. Any capitalized terms that are not defined in the Security Measures have the meaning provided in your Agreement.
1.1. “Agent” means Monte Carlo’s proprietary data observability software that connects to your data warehouses, data lakes, ETLs, and BI tools to extract your metadata, logs and statistics for the provision of the Service.
1.2. “Customer Data” means any data, information, files or other materials and content that you or your end users make available to Monte Carlo in connection with your use of the Service.
1.3. “Personal Data” means any information (i) of an identified or identifiable person and (ii) of an identified or identifiable legal entity (where protected under applicable data protection laws), where such data are provided by you to us in relation to the provision of the Service
1.4. “Data Breach” means a breach of security leading to the accidental or unlawful destruction, loss, alteration, unauthorized disclosure of, or access to Customer Data.
1.5. “Hybrid Deployment” means a customer’s use of the Service where the Agent and/or Object Storage is hosted by customer in the customer’s own environment.
1.6. “Information Security Program” means Monte Carlo’s written security program, policies, and procedures that set forth the administrative, technical, and physical safeguards designed to protect the security of the Service and Customer Data.
1.7. “Monte Carlo Systems” means Monte Carlo’s internal infrastructure, including development, testing, and production environments, for the Service and Software.
1.8. “Privileged User” means a select Monte Carlo employee or third-party contractor who has been granted unique authority to access Customer Data or a customer’s Monte Carlo tenant as required to perform their job function and for Monte Carlo to provide the Service.
1.9. “SaaS Cloud Deployment” means a customer’s use of the Monte Carlo Service where the Agent is deployed and managed by Monte Carlo and hosted in Monte Carlo’s own secure AWS environment.
1.10. “Security Incident Response Plan” means Monte Carlo’s documented protocols for evaluating suspected security threats and responding to confirmed Data Breaches and other security incidents.
1.11. “Service” means as defined in the Agreement and includes both the SaaS and Hybrid Deployment models.
1.12. “Software” means the Monte Carlo data observability and related software used by Monte Carlo and/or provided to you under the Agreement, including but not limited to the Agent and any computer software program, application program interface, or other technology owned by Monte Carlo.
2. Information Security Program Overview
2.1. General. Monte Carlo maintains a comprehensive written Information Security Program (“ISP”) to establish effective administrative, technical, and physical safeguards for the Service and Customer Data, and to identify, detect, protect against, respond to, and recover from security incidents. Monte Carlo’s ISP complies with applicable data protection laws and is aligned with ISO 27001:2022. Additionally, the Monte Carlo Service is certified against SOC 2 Type II. More detailed information on our ISP, including security reports and policies, may be requested at: https://trust.montecarlodata.com/.
2.2. Maintenance and Compliance. Monte Carlo’s ISP is maintained by a dedicated security team, led by our Head of Security and Compliance. Monte Carlo monitors compliance with its ISP and conducts ongoing education and training of personnel to ensure compliance. The ISP is reviewed and updated at least annually to reflect changes to our organization, business practices, technology, services, and applicable laws and regulations. We will not alter or modify the ISP in a way that materially weakens or compromises the effectiveness of its security controls.
2.3. Monte Carlo Personnel Controls.
2.3.1. Background and Reference Checks. Monte Carlo performs industry standard background and/or reference checks as permitted under applicable laws on all Monte Carlo employees as well as any third-party contractor with access to Customer Data or Monte Carlo Systems.
2.3.2. Personnel Obligations. Any Privileged User authorized to access Customer Data is required to commit in writing to information security and confidentiality obligations that survive termination and change of employment. Monte Carlo maintains a formal disciplinary procedure for violations by Monte Carlo personnel of its security policies and procedures.
2.3.3. Training. Upon hire and subsequently at least once per year, all Monte Carlo employees undergo required training on specific security topics, including phishing, insider threats, and the secure handling of Customer Data and personally identifiable information. Further, Monte Carlo implements mandatory, role-specific training for Privileged Users who access Customer Data as part of their job function. Monte Carlo maintains records of training occurrence and content.
2.4. Vendor Management. Monte Carlo maintains and adheres to a documented process for the evaluation and approval of third-party vendors prior to onboarding, which includes appropriate due diligence regarding each third party’s security processes and controls. We require third parties that process, store, or transmit confidential information (including Customer Data) or provide critical services to contractually commit to confidentiality, security responsibilities, security controls, audit, and data reporting obligations.
2.5. Security Contact. If you have security concerns or questions, you may contact us via security@montecarlodata.com.
3. Customer Data
3.1 Collection of Customer Data. Monte Carlo primarily collects and accesses only your metadata, query logs, and configured metrics and does not routinely collect or access Personal Data in the provision of the Service. A summary of the data processed for us to provide the Service is as follows:
| Data Type | Details | Purpose |
| Metadata | Information about tables, schemas, data freshness and volume, names and attributes of BI reports/dashboards, and other such attributes of customer data assets. These data are collected directly from customer warehouses, lakes, and BI tools via APIs, JDBC connections, and other methods. | Build a catalog of warehouse, lake and BI objects along with schema information in order for Monte Carlo to provide the data observability reports and services. |
| Metrics | Row counts, byte counts, last modification date and other similar table-level metrics. These data are collected directly from customer warehouses, lakes, and BI tools via APIs, JDBC connections, and other methods. | Track freshness, volume and other aspects of data health and distribution. |
| Query logs | History of queries, as well as metadata about them (timestamp, user performing the query, errors if any, etc). These data are collected directly from customer warehouses, lakes, and BI tools via APIs, JDBC connections, and other methods. | Track lineage, usage analytics and query history to help with troubleshooting and prevention use cases. |
| Aggregated statistics | Aggregated statistical measures of the data in selected tables. Statistics may include null rates, distinct values, row counts, percentiles, and other similar metrics. These data are collected directly from customer warehouses, lakes, and BI tools via APIs, JDBC connections, and other methods | Track data health and corruption using ML-based anomaly detection as well as customer-provided rules. |
| Data Sampling | A sample set of individual values or data records from the customer tenant in clear text form that are associated with a data reliability incident detected by Monte Carlo. | Help users quickly identify the nature of data issues and their root cause. |
| Application Data | Customer accounts, user settings, configurations, IP address, incidents, and other elements necessary to set up the Service. | This information is generated as users sign up and interact with the Service and for user authentication. |
3.2. Collection of Personal Data. The limited instances in which we may collect and access Personal Data for the provision of our Service include: (i) if Personal Data are included in a query log; (ii) if you opt-in to receive your user performance data via our data reliability dashboard; or (iii) if an anomaly is detected and a Monte Carlo Privileged User views individual data records associated with the particular incident in order to provide customer support as part of our data sampling functionality (“Data Sampling Data”), and Personal Data are included in such data records. We may also collect Application Data that is required for your use of the Service (such as user name and email for registration and authentication purposes), and the access and use of such data are governed by our public Privacy Policy.
3.3. Hosting Location of Customer Data. The Service is a multi-tenant platform that operates on AWS and Customer Data are hosted in AWS environments as Monte Carlo’s subservice organization. AWS provides cloud hosting services, which includes a platform for delivering compute, storage, networking and other infrastructure service to its customers. Customer Data are hosted in either the customer’s or Monte Carlo’s environment, depending on the deployment model used.
3.3.1. Agent. Customer Data that you provide to our Service are moved from your storage environment to the isolated, customer-dedicated Agent, which may be deployed in any of the regions that Monte Carlo supports.Under a Hybrid Deployment you select the region in your own environment where the Agent is deployed. Under a SaaS Cloud Deployment Monte Carlo will make commercially reasonable efforts to deploy the Agent in the AWS region closest to your primary business location, or as you may otherwise direct. The currently available AWS regions for a SaaS Cloud Deployment are listed at: https://docs.getmontecarlo.com/docs/hybrid-solution. More information on the Service architecture for Monte Carlo’s various deployment options is available at: https://docs.getmontecarlo.com/docs/platform-architecture#customer-hosted-agent--object-storage-deployment.
3.3.2. Transfer from Agent. To provide the Service, we transfer Customer Data (excluding row-level Data Sampling Data) from your individual Agent to our Data Monitoring System deployed in our secure AWS environment. Data Sampling Data is never transferred to or stored in our Data Monitoring System, although as detailed in Section 3.2 above, Data Sampling Data may be accessible by authorized Privileged Users via web browser for purposes of providing data sampling support. With respect to such web browser access, such data are only accessible and persists through that browser session.
3.4 Deletion of Customer Data. Monte Carlo maintains a data deletion policy that aligns with SOC 2 Type II standards. Unless otherwise agreed to between the parties in the Agreement, Monte Carlo will delete Customer Data within 90 days after termination of a customer’s account. Monte Carlo will also promptly return or delete any Customer Data in our possession or control upon the customer’s written request.
4. Encryption.
4.1. Encryption of Customer Data. All Monte Carlo network traffic is protected by Transport Layer Security (TLS), which is enabled by default and cannot be disabled. Customer Data (including any Personal Data) are at all times encrypted in transit using TLS 1.2+ cipher suites and a minimum key length of 128 bits. Customer Data (including any Personal Data) are at all times encrypted at rest using AES-256-bit (or better) encryption.
4.2. Key Management Procedures for Encryption. All encryption both at rest and in transit conforms to ISO 27001:2013. Keys to decrypt are held by Monte Carlo and AWS and the ability to re-identify is held solely by Monte Carlo. We maintain documented cryptography and key management guidelines for the secure transmission of Customer Data, and we configure our TLS encryption key protocols and parameters accordingly. Monte Carlo’s key management procedures include: (i) generation of keys with approved key length; (ii) secure distribution, activation and storage, recovery and replacement, and update of keys; (iii) recovery of keys that are lost, corrupted, or expired; (iv) backup/archive of keys; (v) maintenance of key history; (vi) allocation of defined key activation and deactivation dates; (vii) restriction of key access to authorized individuals; and (viii) compliance with legal and regulatory requirements. When a key is compromised, it is revoked, retired, and replaced to prevent further use (except for limited use of that compromised key to remove or verify protections). Keys are protected in storage by encryption and are stored separately from encrypted data. TLS certificates are obtained from a major, widely trusted third-party public certificate authority. In the course of standard TLS key negotiation for active sessions, ephemeral session keys are generated which are never persisted to disk, as per the design of the TLS protocol.
5. System and Network Security.
5.1. Access Controls.
5.1.1. Monte Carlo uses read-only access via APIs and/or dedicated service accounts to access Customer Data. Monte Carlo accesses your Monte Carlo tenant from a single source IP dedicated to that particular customer, allowing the customer to protect access to its data resources at the network level.
5.1.2. Privileged User Access. As a general matter, Monte Carlo personnel do not have authorization to access your Monte Carlo tenant. Only a small group of Privileged Users are authorized to access your tenant in rare cases such as to provide troubleshooting or support. Monte Carlo adheres to the principle of “least privilege” with respect to those Privileged Users, any access is limited to the minimum time and extent necessary. Privileged Users may only access your Monte Carlo tenant via the Service’s web interface and requires approval by Monte Carlo senior management.
5.1.3. Access Review and Auditing. Monte Carlo reviews Privileged User access authorization on a quarterly basis. Additionally, we revoke a Privileged User’s access when it is no longer needed, including within 24 hours of that Privileged User changing roles or leaving the company. We also log any access by Monte Carlo personnel to your Monte Carlo tenant. Audit logs are retained for at least six years, and include a timestamp, actor, action, and output. Monte Carlo utilizes a combination of automated and human review to scan those audit logs.
5.1.4. Monte Carlo Personnel Access to Monte Carlo Systems. Our policies and procedures regarding access to Monte Carlo Systems adhere to the principles of role-based access control (RBAC), least privilege, and separation of duties. In accordance with these principles, with respect to the Service, Monte Carlo developers are only granted access to our development environments, and access to our production environment is limited to Privileged Users with appropriate authorizations. We review access authorizations to Monte Carlo Systems on a quarterly basis and we review any changes to authorizations for Privileged Users immediately. As part of the employee off-boarding process, access to Monte Carlo Systems is revoked within 24 hours of an employee’s departure.
5.1.5. Access to Monte Carlo Service Production Environment. Our backend production environment that runs Monte Carlo Service is only accessible by a dedicated group of Privileged Users whose privileges must be approved by senior management. Privileged Users may only access our backend production environment via a private VPN and doing so requires MFA both to log in and to establish a connection to the internal infrastructure.
5.1.6. Credential Requirements. All Monte Carlo personnel passwords must conform to industry-standard complexity rules. Additionally, MFA is mandatory for all Monte Carlo personnel and cannot be disabled.
5.2. Endpoint Controls. For access to Customer Data or Monte Carlo Systems, Monte Carlo personnel use Monte Carlo-issued laptops that are managed by a Mobile Device Management Platform (MDM). Security controls are enforced by MDM and include but are not limited to: (i) full disk encryption; (ii) no USB storage device usage; (iii) users are not running with administrative privileges; (iv) and endpoint detection and response (EDR) tools to monitor and alert for suspicious activities and Malicious Code (as defined in Section 8 below).
5.3. Firewalls. Monte Carlo laptops are required to run a host-based firewall to prevent unauthorized applications and services from accepting incoming network connections.
5.4. Hardening. Monte Carlo laptops have been hardened in accordance with NIST guidelines and enforced by MDM. Hardening processes include but are not limited to: (i) turning off unnecessary services; (ii) password protected screensaver; (iii) enforcing complex password requirements; (iv) and routine patching.
5.5. Monitoring and Logging. Monte Carlo laptops send activity and audit logs to a centralized logging server that is routinely monitored for anomalous behavior or indicators of compromise.
6. Physical and Environmental Controls.
6.1. AWS Data Centers. The Monte Carlo Service runs on secure servers hosted by Amazon Web Services. AWS is responsible for the security of its data centers, which are compliant with a number of physical security and information security standards detailed at the AWS website: https://aws.amazon.com/security/. At least twice per year, AWS is subject to due diligence performed by Monte Carlo or third-party auditors, which includes obtaining and reviewing security compliance certifications.
6.2. Monte Carlo Offices. We ensure that all of our Monte Carlo offices follow industry best practices to employ physical security controls that are appropriate to the level of risk posed by the information stored and the nature of operations at our offices. No Customer Data is hosted on systems located at Monte Carlo offices.
7. Monte Carlo Systems Security.
7.1. Separation of Production and Non-Production Environments. Monte Carlo Service has strict separation between production and non-production environments. Our Monte Carlo Service production environment and your Customer Data are never utilized for non-production purposes. Our non-production environments are utilized for development, testing, and staging. Monte Carlo also maintains firewalls to achieve strict separation of our Monte Carlo Service production environment and Monte Carlo’s internal network.
7.2. Software Development Lifecycle. Monte Carlo has a dedicated security team, reporting to the Head of Security and Compliance, that leads security initiatives in the software development lifecycle (SDLC). We develop new products and features in a multistage process using industry standard methodologies that include defined security acceptance criteria and align with NIST and OWASP guidance. The SDLC includes regular code reviews, documented policies and procedures for tracking and managing all changes to our code, continuous integration of source code commits, code versioning, static and dynamic code analysis, vulnerability management, threat modeling, and bug hunts, as well as automated and manual source code analysis.
7.3. Monitoring and Alerting. Monte Carlo monitors the health and performance of Monte Carlo Service without needing to access your environments or Customer Data. Monte Carlo maintains a centralized log management system for the collection, storage, and analysis of log data for our Monte Carlo Service production environment and your Monte Carlo environments. We use this information for health monitoring, troubleshooting, and security purposes, including intrusion detection. We utilize a combination of automated scanning, automated alerting, and human review to monitor the data.
8. Vulnerability Management.
8.1. Monte Carlo Service Vulnerability Scanning. Monte Carlo maintains a documented vulnerability enumeration and management program that leverages automated MDM and other advanced threat detection tools to monitor and alert for suspicious activities, potential malware, viruses, and/or malicious computer code (collectively “Malicious Code”). We conduct at least weekly scans of all product systems upon which Monte Carlo Service is deployed, as well as all third-party code integrated into our products. Monte Carlo’s vulnerability management policy requires individual engineering teams to identify known vulnerabilities in system components and develop remediation timeframes commensurate with the severity of an identified issue. We also utilize automated tooling in conjunction with monitoring security bulletins for relevant software and libraries and implement patches if security issues are discovered. We do not monitor Customer Data for Malicious Code.
8.2. Vulnerability Remediation. Monte Carlo uses a company-wide ticketing system for all security issues to assess priority level and track issues until remediation. We implement patches to our operating system and applications on a need-to-update basis, as determined in accordance with the Common Vulnerability Scoring System (CVSS) and our established internal service level timelines for addressing identified vulnerabilities based on priority level. Development tasks for all patches, bug fixes, and new features are defined as issues for specific target releases and are deployed to production only after completing requisite checkpoints, including quality assurance testing, staged deployment, and management review.
8.3. Penetration Testing and Internal Risk Assessments. Monte Carlo Service undergoes regular reviews from both internal and external security teams.
8.3.1. External Testing. Our Monte Carlo Service production environment is subject to an external penetration test by a nationally recognized security firm at least once per calendar year. Upon request, we will provide you with a summary letter of engagement that includes the number of high, medium, and low issues identified, but due to the sensitivity of the information gathered during these tests, we cannot allow customers to perform testing of our production platform. Application-level security testing uses a standard application assessment methodology (e.g., OWASP). Additionally, external engagements with security consultants may include social engineering and phishing testing.
8.3.2. Internal Testing. Internally, Monte Carlo Service undergoes periodic risk assessments, including technical vulnerability discovery and analysis of business risks and concerns. The Monte Carlo security team is also routinely involved in source code review, architecture review, code commit peer review, and threat modeling.
9. Business Continuity and Disaster Recovery.
Monte Carlo maintains documented business continuity and disaster recovery plans (collectively “BCDR”) that aligns with ISO/IEC 22301:2019. Our BCDR plans include: (i) clearly defined roles and responsibilities; (ii) decision-maker line of succession planning; (iii) availability requirements for customer services; and (iii) backup and restoration procedures. We review, update, and test our BCDR plan at least annually.
10. Incident Response and Communications.
10.1. Security Incident Response Plan. As part of the ISP, Monte Carlo maintains an established Security Incident Response Plan that aligns with ISO/IEC 27001:2013. In the event that Monte Carlo becomes aware of a Data Breach or other security incident, Monte Carlo will follow the Security Incident Response Plan, which includes: (i) clearly defined roles and responsibilities, including designation of an Information Security Manager; (ii) reporting mechanisms; (iii) procedures for assessing, classifying, containing, eradicating, and recovering from security incidents; (iv) procedures for required notifications to relevant authorities and customers; (v) procedures for forensic investigation and preservation of event and system log data; and (vi) a process for post-incident and resolution analysis designed to prevent future similar incidents. The Security Incident Response Plan is reviewed, updated, and tested annually.
10.2. Security Incident Tracking. We maintain a comprehensive security incident tracking system that aligns with ISO/IEC 27001:2013 and documents: (i) incident type and suspected cause; (ii) whether there has been unauthorized or unlawful access, disclosure, loss, alteration, or destruction of data; (iii) if so, the categories of systems and/or data affected by the incident, including categories of personal information; (iv) the time, date and location of the incident; and (v) the remediation actions taken.
10.3. Customer Communications. We will notify you without undue delay if we become aware of any confirmed Data Breach, and in any case, where feasible, within 72 hours after becoming aware. Taking into account the information available to us, such notice will include a description of the nature and cause of the Data Breach and the expected resolution time. To the extent possible, we will subsequently update you with information regarding evaluation of the root cause, potential impact, remediation actions taken, and actions planned to prevent a future similar event.
11. Audit Reporting.
11.1. Third-Party Certifications and Audit Reports. Upon request, and subject to the confidentiality obligations set forth in the Agreement, we will make available to you (or your independent, third-party auditor) information regarding Monte Carlo’s compliance with the security obligations set forth in these Security Measures in the form of third-party certifications and audit reports (e.g., SOC 2 Type II).
11.2. Security Questionnaires. No more than once per year, we will complete a written security questionnaire provided by you regarding the controls outlined in these Security Measures.
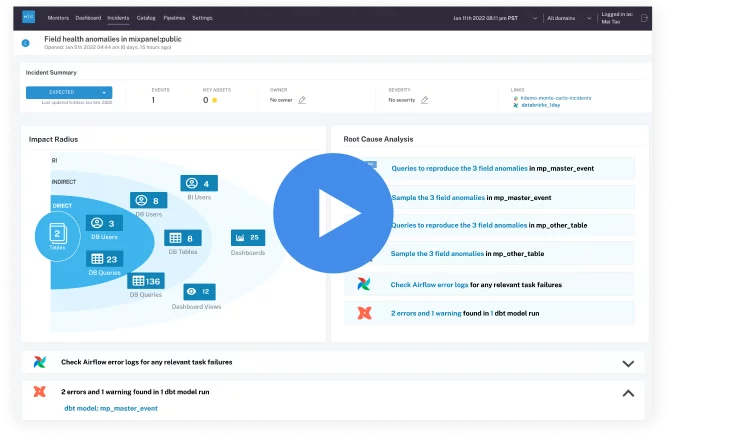 Product demo.
Product demo. 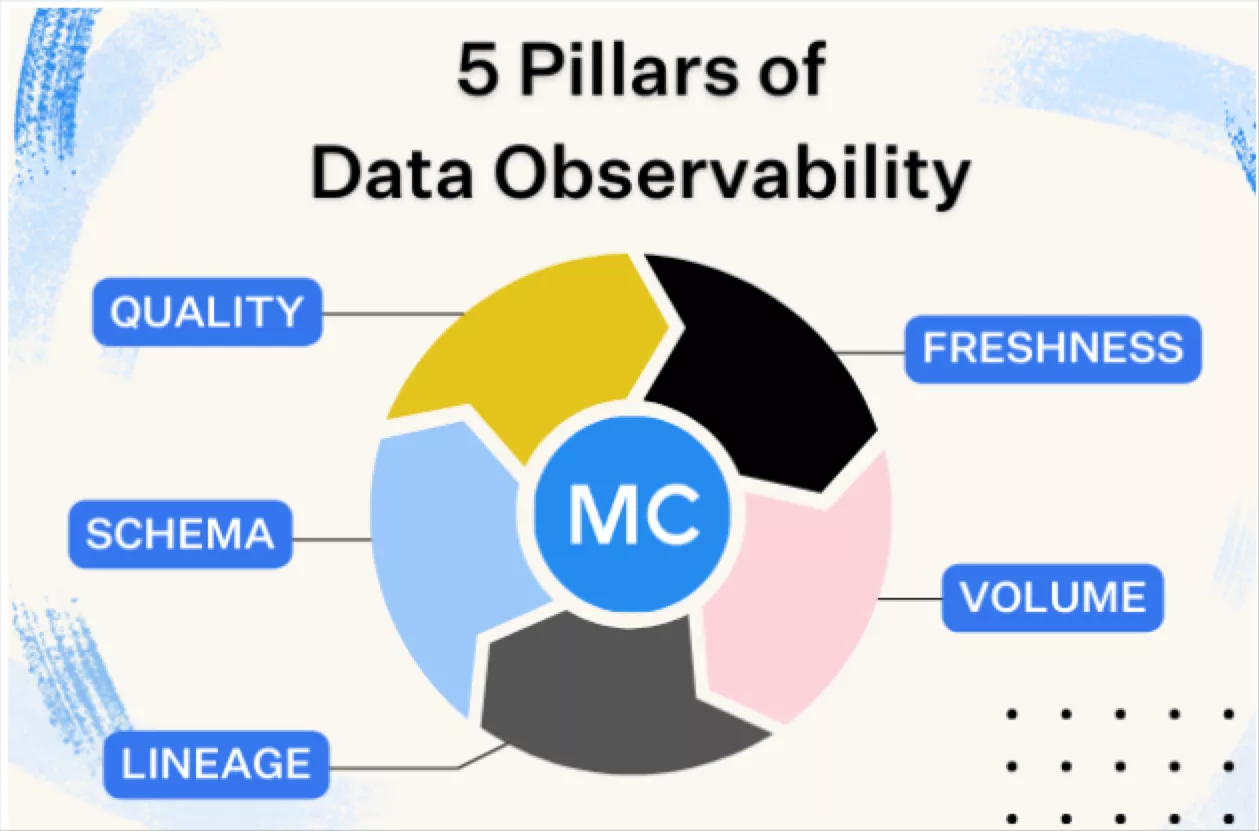 What is data observability?
What is data observability? 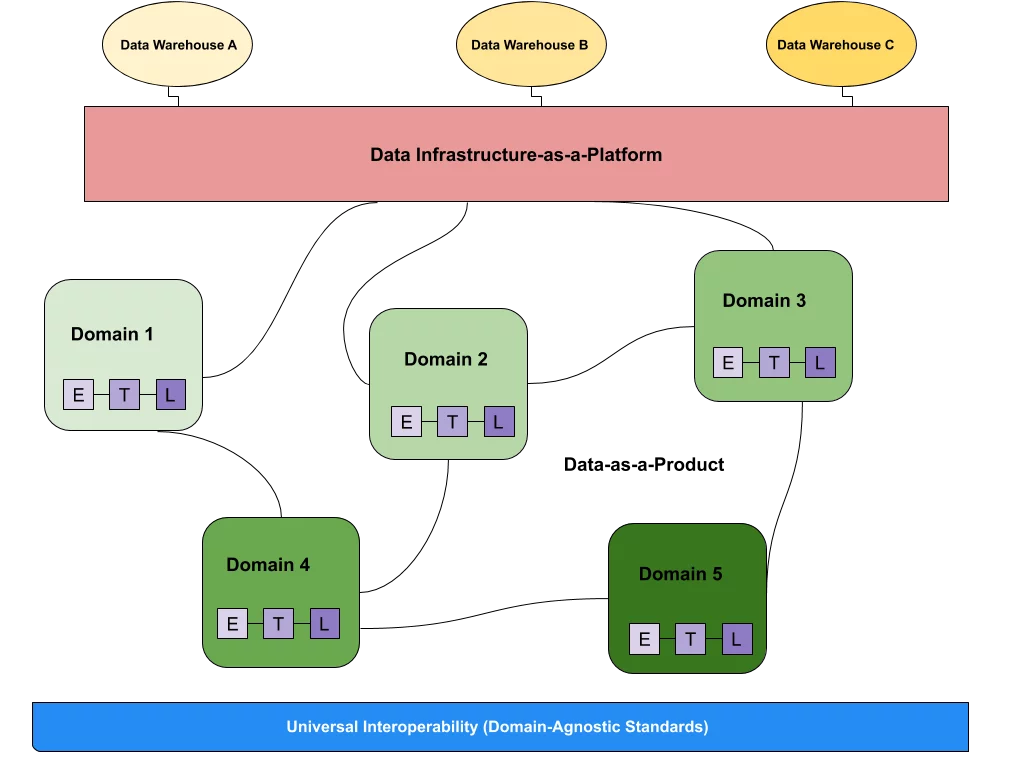 What is a data mesh--and how not to mesh it up
What is a data mesh--and how not to mesh it up 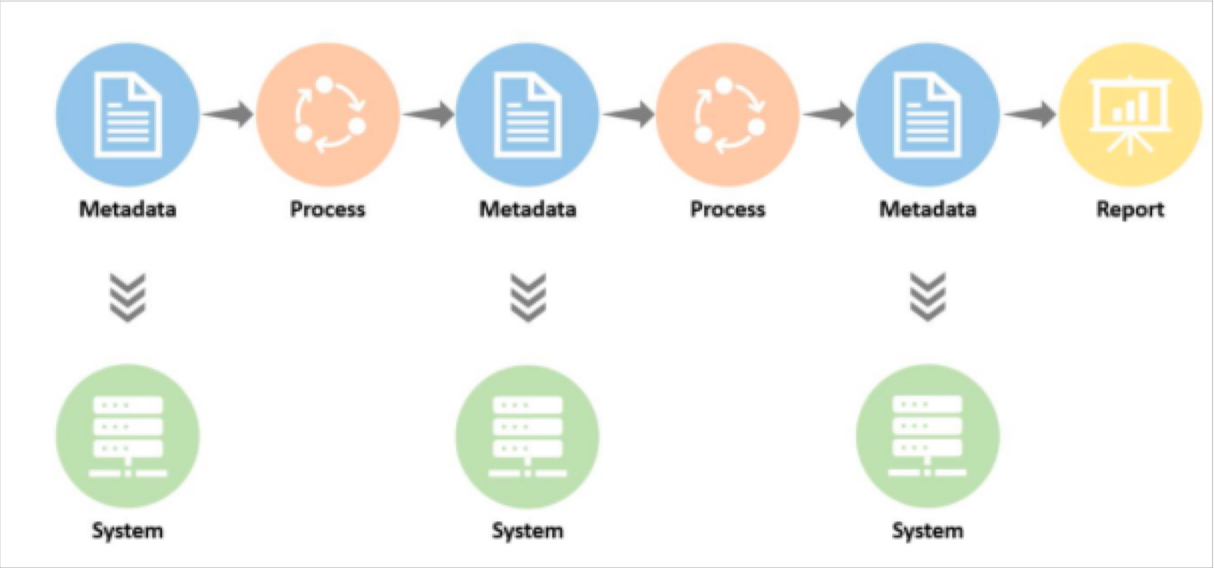 The ULTIMATE Guide To Data Lineage
The ULTIMATE Guide To Data Lineage